Welcome to the first edition of LGA Monthly Security Bytes!
Here, you’ll find bite-sized security developments and practical insights to help you stay ahead of day-to-day security operations.

Over the past month, we saw a surge in critical, internet-exploitable vulnerabilities, with many scoring CVSS 9.8-10.0. Several enable unauthenticated remote code execution, while others stem from legacy systems and exposed configurations.
In parallel, government-impersonation scams continue to rise locally, relying on urgency and fear rather than technical exploits.
The pattern is clear: security risk today is driven as much by operational gaps as by the software vulnerabilities themselves.
These vulnerabilities enable unauthenticated attackers to execute code, bypass authentication or gain system-level access over the internet, making exposure immediate and high impact.
|
These risks arise from unsupported hardware, insecure defaults, or exposed management interfaces, often overlooked in day-to-day operations.
|
Our security solutions are designed to reduce exposure across endpoints, networks and applications through continuous visibility and proactive response.
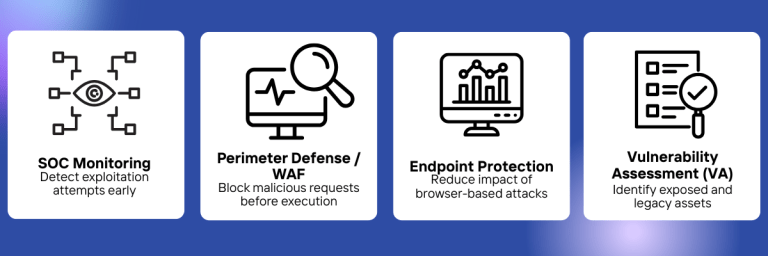
Understand what truly matters with insights from our local SOC team before it becomes an incident

All-in-One IT Solutions: Secure, Connected and Cloud-Ready with LGA
© 2025 LGA Telecom Pte Ltd. All Rights Reserved.
